Project Glasswing: Why Anthropic Limits Mythos
Project Glasswing is Anthropic's restricted-access program for Claude Mythos Preview — focused exclusively on defensive cybersecurity. Here's what it is and why it exists.

I’ve been tracking Anthropic’s model releases for a while now, and the April 7 announcement was the first one that genuinely made me stop and reread it twice.
Not because Claude Mythos Preview is “powerful” — that word’s been applied to every model release for two years. But because Anthropic did something unusual: they built a capability, concluded it was too risky to release, and instead structured a restricted program specifically designed to use that capability for defense before attackers figure out they’re behind. That’s a different kind of move. Project Glasswing is worth understanding clearly — not as a PR story, but as a window into how frontier AI governance is actually playing out.
I’m your friend, Dora. Here’s what’s confirmed, what it means, and what builders should take from it.
What Project Glasswing Is
Anthropic’s managed access program for Claude Mythos Preview
Project Glasswing is Anthropic’s initiative to deploy Claude Mythos Preview — their most capable model to date — specifically for defensive cybersecurity work. The model isn’t publicly available. Access is restricted to a curated group of organizations working on critical software infrastructure.
The launch partners named by Anthropic include AWS, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, NVIDIA, and Palo Alto Networks. Beyond those named partners, Anthropic has extended access to over 40 additional organizations that build or maintain critical software infrastructure.
Purpose: give defenders a head start
The framing Anthropic uses is explicit: the same capabilities that make AI models dangerous in the wrong hands make them invaluable for finding and fixing flaws in important software — and for producing new software with far fewer security bugs.
That’s the whole thesis. A model that can find zero-day vulnerabilities autonomously is simultaneously the most useful security tool ever built and one of the most dangerous offensive capabilities ever created. Project Glasswing is the attempt to let the defense side run first.
What’s already been found
This isn’t speculative. Over the past few weeks, Anthropic used Claude Mythos Preview to identify thousands of zero-day vulnerabilities — flaws previously unknown to the software’s developers — many of them critical, in every major operating system and every major web browser, along with a range of other important pieces of software.
One specific example from the Anthropic Frontier Red Team blog: Mythos Preview fully autonomously identified and exploited a 17-year-old remote code execution vulnerability in FreeBSD (CVE-2026-4747) that allows anyone to gain root on a machine running NFS — starting from an unauthenticated position anywhere on the internet. No human was involved after the initial prompt.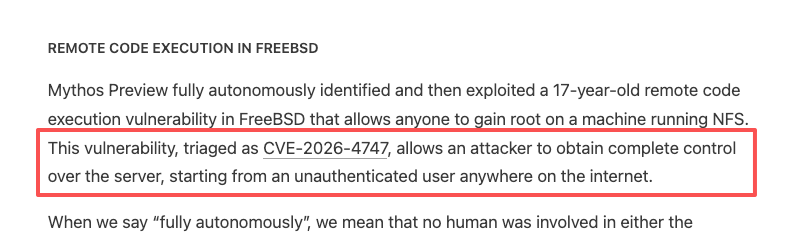
The 90-day commitment
This is the detail most coverage has underplayed. Anthropic has committed explicitly: within 90 days, they will report publicly on what they’ve learned, as well as the vulnerabilities fixed and improvements made that can be disclosed. That’s a time-bound public commitment — not a vague “we’ll share learnings eventually.” It means by early July 2026, there should be a real accounting of what this program found and fixed.
Why Anthropic Chose This Approach
The dual-use problem, stated plainly
This is the core logic, and it’s worth sitting with it. A model that can autonomously find and exploit software vulnerabilities isn’t just a powerful security tool — it’s a powerful attack tool. The capability doesn’t come with an intent detector. Broadly releasing Mythos Preview means broadly releasing the ability to compromise critical infrastructure.
That’s the dual-use problem. It’s not that Anthropic doesn’t trust developers. It’s that a broadly available model capable of chaining zero-days and writing working exploits creates a risk profile that no responsible actor can ignore — regardless of who’s asking. The system card for Mythos Preview states it directly: “Claude Mythos Preview’s large increase in capabilities has led us to decide not to make it generally available."
"Strikingly capable” — and what that actually means
Anthropic’s language here is deliberate. They didn’t call Mythos Preview “incrementally better at security tasks.” The word they used is “strikingly capable.” The model can single-handedly perform complex, effective hacking tasks — identifying multiple undisclosed vulnerabilities, writing code to exploit them, and chaining those together to penetrate complex software.
Mythos Preview has also effectively saturated the existing internal and external benchmarks Anthropic used to track model capabilities, which forced a shift to testing against novel real-world tasks. When your model outgrows your eval suite, you’re in genuinely new territory.
What this restriction explicitly is not
It’s worth being precise here because the framing matters. This is not Anthropic hoarding capabilities. It’s not a competitive play. The restriction exists because the asymmetry of harm from broad release skews sharply negative in the near term: defenders need coordination and time to patch; attackers only need the model.
By releasing this model initially to a limited group of critical industry partners, Anthropic aims to enable defenders to begin securing the most important systems before models with similar capabilities become broadly available.
The logic is sequencing, not secrecy.
What Glasswing Participants Are Doing
Scope of work
Partners are using Claude Mythos Preview specifically for defensive security — finding and fixing vulnerabilities in systems they own or maintain. The scope extends to first-party codebases and open-source systems. The Linux Foundation’s inclusion is notable precisely because so much critical infrastructure runs on open-source software that historically has been under-resourced for security.
What partners are saying
Cisco’s statement from the official Glasswing page: the work has shown they can identify and fix security vulnerabilities across hardware and software at a pace and scale previously impossible. Microsoft noted the model is already helping strengthen code in critical codebases. AWS described applying it across a technology stack that handles over 400 trillion network flows daily.
These aren’t demo testimonials. These are production security teams describing actual usage.
The resource commitment
Anthropic has committed $100M in model usage credits for Project Glasswing participants throughout the research preview, along with $4M in direct donations to open-source security organizations. Access is priced at $25/$125 per million input/output tokens via the Claude API, Amazon Bedrock, Google Cloud’s Vertex AI, and Microsoft Foundry.
What This Tells Us About Anthropic’s Release Strategy
Safety-gated releases are now real
Before Glasswing, “we’ll be cautious about releasing this” was mostly theoretical language. Now it’s operational. Anthropic built a capability, evaluated it, decided the risk profile precluded general availability, and structured an alternative that still creates value while managing the downside. That’s a template.
The practical implication: not every frontier capability will follow a public API release. Some capabilities — particularly those with obvious dual-use potential — may be gated behind managed programs, with access conditioned on organizational type, use case, or security posture.
How this differs from a standard beta
A normal API beta is about readiness: the model isn’t quite stable, documentation is incomplete, you need feedback before general release. Glasswing is categorically different. The model is ready. The issue is what happens if it’s broadly deployed before defenders have had time to use it. The restriction is about sequencing impact, not technical maturity.
This distinction matters for how you think about what “access” to frontier models means going forward.
What comes after Glasswing
Anthropic has stated they do not plan to make Mythos Preview generally available. Their stated goal is to eventually enable safe deployment of Mythos-class models at scale — but that requires developing cybersecurity safeguards that can detect and block the model’s most dangerous outputs. They plan to launch new safeguards with an upcoming Claude Opus model, using it to improve and refine those safeguards with a model that doesn’t carry the same risk profile.
Translation: there’s a safety development roadmap that has to precede broader access. The 90-day public report will be the first real data point on whether that roadmap is progressing.
Implications for Builders and the Ecosystem
What gated frontier models mean for you
If you’re building on AI — whether as an infra lead, product owner, or technical founder — Glasswing is the first concrete signal that the access model for frontier capabilities is bifurcating. Public APIs will continue to carry most use cases. But for capabilities at the frontier of dual-use risk, managed access programs with organizational vetting may become standard.
That’s not necessarily bad for builders. The alternative — no access — is worse. But it does mean the path to frontier capabilities for sensitive domains will increasingly require demonstrating organizational fit, not just technical readiness.
What Glasswing signals about future high-capability models
The pattern Anthropic has established with Glasswing will almost certainly be applied again. When a future model demonstrates capabilities that create meaningful dual-use risk — whether in biology, chemistry, cyber, or other domains — expect the same sequencing: restricted access to defenders and researchers, a defined transparency timeline, and public reporting before any broader rollout.
Anthropic has noted this work may take years, and that frontier AI capabilities are likely to advance substantially over that time. This is not a one-time edge case. It’s the beginning of a governance pattern.
FAQ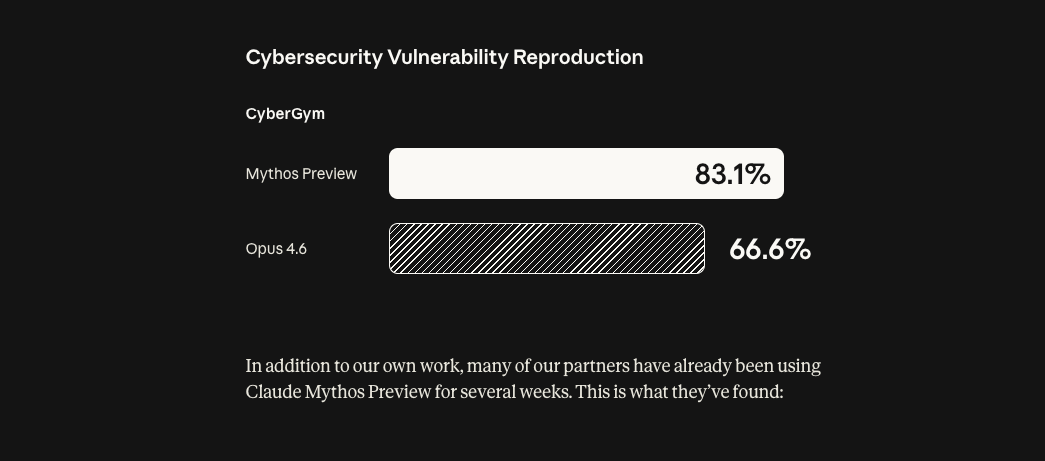
Who qualifies for Project Glasswing access?
The current scope covers two groups: named launch partners (large tech and security companies listed publicly by Anthropic) and over 40 additional organizations that build or maintain critical software infrastructure. There’s no public application process described on the official Glasswing page as of this writing.
Can I apply for Glasswing as an independent researcher?
The current framing is organizational, not individual. Independent researchers aren’t excluded in principle — open-source maintainers are mentioned explicitly — but the access pathway is through organizations maintaining critical software, not individual researchers. If this changes, it would likely be announced via the official Glasswing page.
Will Claude Mythos eventually become publicly available?
Anthropic has stated they do not plan to make Mythos Preview generally available. A future model with Mythos-class capabilities may become available once the requisite safety safeguards are developed and validated — but there’s no public timeline on that.
What makes Mythos different enough to require restricted release?
Two things: autonomous capability and scope. Previous models could assist with security tasks. Mythos Preview can chain vulnerabilities, write working exploits, and identify previously unknown bugs across every major OS and browser — without human involvement after the initial prompt. That’s a qualitatively different risk profile.
Has Anthropic done this kind of gated release before?
Not at this scale or with this explicit safety framing. Previous restricted releases were standard betas or enterprise programs. Glasswing is the first case where Anthropic has publicly said: this capability is too dangerous to release broadly, and here’s the structured alternative. That’s new.
More to come — the 90-day public report is the next real data point. Worth watching.
Previous posts: