What Is claw-code? The Claude Code Rewrite Explained
claw-code is a clean-room Python rewrite of Claude Code's agent harness. Here's what it is, how it happened, and what builders need to know.
Hey, guys. I’m Dora. Can you imagine? I’ve been watching the claw-code repository since the morning it appeared. Not because I expected to use it — but because the circumstances around its creation clarify how the agentic coding ecosystem actually works, underneath all the noise.
Let me walk through what happened, what claw-code is, and who should actually care.
What Happened: The Claude Code Source Exposure
How the Source Map Leak Occurred
On March 31, 2026, security researcher Chaofan Shou noticed something odd in the npm registry. Version 2.1.88 of @anthropic-ai/claude-code had shipped with a 59.8 MB JavaScript source map file attached.
Source maps are debugging artifacts — they translate minified production code back into readable TypeScript so developers can make sense of stack traces. They are not supposed to ship in public packages.
The mechanism isn’t exotic. Bun’s bundler, which Claude Code uses internally, generates source maps by default unless you explicitly disable them. There’s an open Bun bug (oven-sh/bun#28001, filed March 11) reporting that source maps appear in production builds even when they shouldn’t. If that’s what caused the leak, then Anthropic’s own build toolchain shipped a known issue that exposed their own product. Nobody had to hack anything. The file was just there, pointing to a zip archive sitting on Anthropic’s own Cloudflare R2 storage bucket.
Anthropic confirmed the incident as “a release packaging issue caused by human error, not a security breach.” Worth noting: this is the second time it’s happened — a nearly identical source map leak occurred with an earlier version in February 2025.
One more thing for anyone who updated Claude Code via npm that morning: a separate supply-chain attack on the axios package was active between 00:21 and 03:49 UTC the same day. Axios is a Claude Code dependency. If you updated during that window, audit your dependencies and rotate credentials.
What Was Actually Exposed
No customer data, no API credentials, no model weights. What was exposed: approximately 512,000 lines of TypeScript across ~1,900 files — the query engine, tool system, multi-agent orchestration logic, context compaction, and 44 feature flags covering functionality that’s built but not yet shipped.
Those feature flags are the most strategically sensitive part. Compiled code sitting behind flags that evaluate to false in the external build isn’t just implementation detail — it’s a product roadmap. Competitors can now see what Anthropic has built and is considering shipping. That strategic surprise can’t be un-leaked.
What Is claw-code?
Clean-Room Rewrite, Not an Archive
Within hours of the exposure, mirrored repositories appeared on GitHub. Anthropic began issuing DMCA takedowns. The internet did not wait.
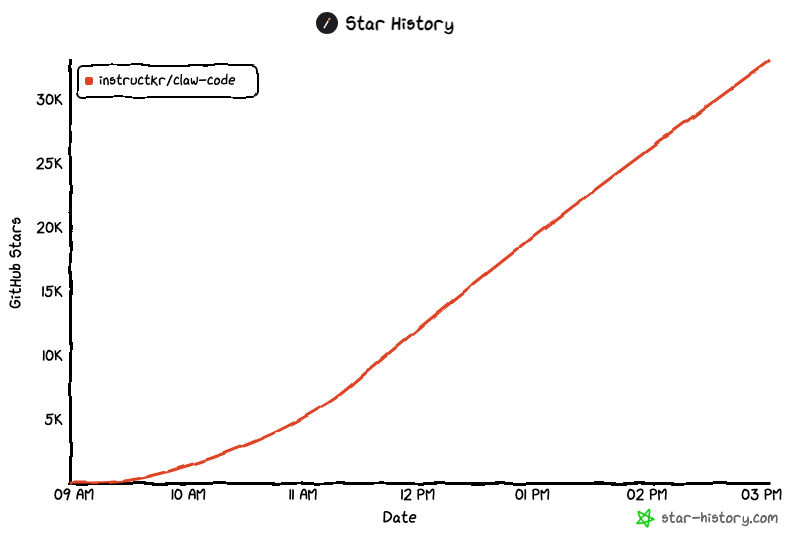
Sigrid Jin (@instructkr) — a Korean developer who had attended Claude Code’s first birthday party in San Francisco in February — published what became claw-code. The repo reached 50,000 stars in two hours, one of the fastest accumulation rates GitHub has recorded.
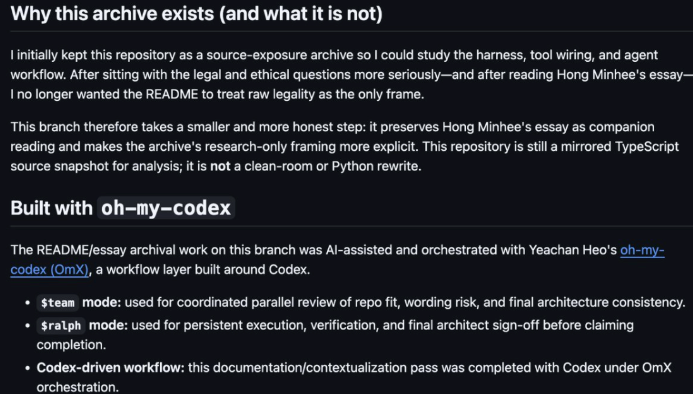
The important distinction: claw-code is not an archive of the leaked TypeScript. It’s a clean-room Python rewrite, built from scratch by reading the original harness structure and reimplementing the architectural patterns without copying Anthropic’s proprietary source. Jin built it overnight using oh-my-codex, an orchestration layer on top of OpenAI’s Codex, with parallel code review and persistent execution loops.
Whether clean-room reimplementation fully sidesteps copyright exposure is a legal question, not a technical one. That answer isn’t settled. The repo is explicit: “This repository does not claim ownership of **the original Claude Code source material.**” But framing and legal outcome aren’t the same thing.
Current State: Python Now, Rust Later
As of April 2026, the main source tree is Python-first. The structure mirrors Claude Code’s core modules: CLI entry, query engine, runtime session management, tool execution, permission context, session persistence, and a parity_audit.py that explicitly tracks gaps from the original implementation.
That last file is worth noting. It’s built-in honest accounting of what the rewrite hasn’t caught up to yet. That kind of transparency is more useful than pretending completeness.
A Rust port is in progress — described in the README as the next direction. No stable release, no confirmed timeline.
What the Architecture Reveals
The real value here — for builders — isn’t the drama. It’s what the exposed architecture tells us about how production-grade agentic coding systems are actually structured.
Multi-Agent Orchestration Patterns
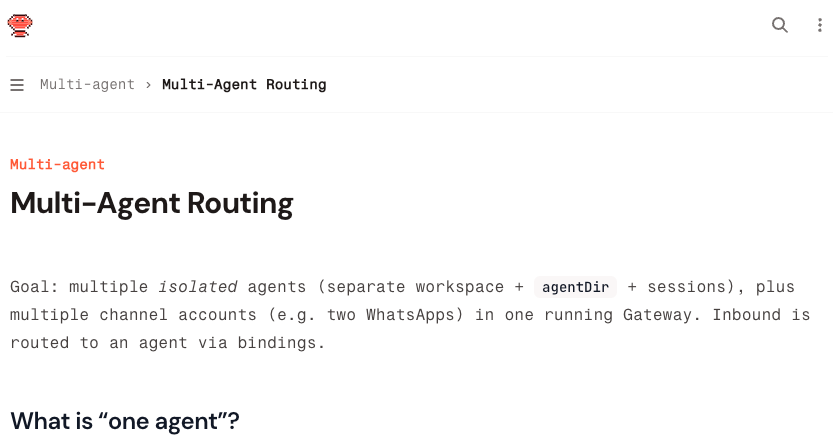
Claude Code isn’t a single chatbot loop. The community analysis that’s spread widely since the leak describes its core: one agent loop, 40+ discrete tools, on-demand skill loading, context compression, subagent spawning, a task system with dependency graphs, and worktree isolation for parallel execution.
The subagent pattern is worth understanding. When a task risks filling the primary context window, Claude Code spawns independent agent instances with their own context and task scope. Exploratory work doesn’t contaminate the main thread. Tasks run in parallel without blocking each other.
What’s notable is how minimal the orchestration layer is. It doesn’t impose rigid workflows. It provides tools, manages permissions and context, and gets out of the way. The model does the reasoning. The harness creates conditions for that reasoning to be useful.
Permission Layers and Tool Sandboxing
Forty-plus tools — bash execution, file reads, web fetch, LSP integration, git operations — are each permission-gated individually. Compound bash commands chained with &&, ||, ;, or pipes are evaluated sub-command by sub-command. If any part would be denied, the whole command is blocked.
The deny list always wins over the allow list. That’s the right design for anything executing arbitrary shell commands.
This architectural instinct is converging across the ecosystem. The OpenClaw multi-agent routing documentation describes per-agent tool policies, session isolation, and separate auth profiles — the same patterns, applied to a different host platform. An agent with broad permissions and no sandboxing is an agent you can’t trust with real work. The field is figuring this out.
Should Builders Pay Attention to claw-code?
Experimental vs. Production Use
If you’re studying agentic harness design — how to structure tool permissions, how context compaction works, how subagent spawning is coordinated — claw-code is genuinely useful. The Python implementation is readable, parity_audit.py gives you a map of where it diverges from the original, and the architecture is now well-documented across multiple independent analyses.
If you’re building something to ship or depend on, the picture is different. The Python rewrite is less than a week old. The Rust port is aspirational. There’s no versioning stability, no maintenance commitment, and no clarity on how legal exposure might affect the project’s continuity. Depending on claw-code in production means betting on a project that could change significantly — or disappear — based on factors outside your control.
For most builders right now: read the code, don’t run it in production.
Legal and Stability Risks to Consider
Anthropic’s DMCA actions against archives of the original TypeScript are active. The legal status of claw-code as a clean-room rewrite is genuinely unclear. Clean-room reimplementation has a legal history that sometimes protects projects and sometimes doesn’t, depending on specifics. Anyone building on this should factor that uncertainty in honestly.
The stability question is separate. Even if the project continues unimpeded, a codebase built in a single overnight session is not at parity with what it’s modeling. The parity_audit.py tracks the gaps — but tracking gaps isn’t the same as closing them.
FAQ
Q: Is claw-code the same as Claude Code? No. Claude Code is Anthropic’s official TypeScript CLI, actively maintained, distributed via npm. claw-code is an independent Python rewrite that mirrors architectural patterns. Same design philosophy; different project entirely.
Q: Can I replace Claude Code with claw-code? Not today. claw-code isn’t at feature parity, the Rust port isn’t stable, and it carries unresolved legal questions. For actual coding work, Claude Code remains the production tool.
Q: What does Anthropic’s DMCA action mean for the project? Anthropic has targeted repositories hosting the original leaked TypeScript. claw-code claims clean-room status as its defense. Whether that holds up legally is unresolved. The project could face pressure regardless.
Q: Is claw-code open source? It’s published on GitHub under a permissive license. Whether “open source” and “safe to depend on” are the same thing here is a question worth sitting with.
The architectural exposure from this incident matters more to me than claw-code itself. Claude Code’s internal design — subagent spawning, tool sandboxing, context compaction, permission layering — is now documented in public analysis well beyond what reverse engineering had previously surfaced. That raises the baseline for anyone building in this space.
Whether claw-code finds stable footing — legally and technically — I genuinely don’t know. For now: read it, don’t deploy it.
Previous posts: